Choosing the right cloud platform for your deployment planning is no longer just an IT decision; it is a central component of your risk management. For one GDPR-compliant deployment planning You have to rely on providers who fully comply with strict data protection laws such as the GDPR and the stricter Swiss data protection law (revDSG). This is the only way to avoid serious fines and personal liability risks.
Why data protection decides everything when planning operations in the cloud

Every day you juggle highly sensitive employee data - from availability and shift schedules to wage information. But have you ever wondered where this data actually resides and who could access it? The answer to this question has direct and harsh consequences for the security of your company.
An ill-advised choice of cloud platform can quickly prove to be an extremely expensive mistake. The legal requirements have not only increased in recent years, they have exploded.
The new Swiss data protection law worsens the situation dramatically
In Switzerland in particular, the situation has become extremely serious. The revised Swiss Data Protection Act (revDSG), since September 1, 2023 in force, marks a real turning point. It replaces a regulation that is over 30 years old and entails massive tightening, especially in terms of penalties.
Personal liability is particularly serious: the person responsible for a violation must personally up to 250,000 CHF pay penalty. The company itself is only partly liable 50,000 CHF, if no responsible party can be identified. This development shows how seriously the legislature now takes the protection of personal data. For you this means: Ignorance does not protect you from punishment.
The cloud is much more than just storage space
Your cloud infrastructure is the foundation on which your entire operational planning rests. It determines how well your data is really protected from unauthorized access, data leaks or cyber attacks.
The right cloud platform not only secures your data, but also the future of your company. A wrong decision can lead to loss of reputation, large fines and the ultimate loss of customer trust.
Imagine you are planning to deploy security personnel for a large event. In the cloud you not only store names and shifts, but also qualifications, addresses and maybe even health data. A data leak would not only violate the GDPR, but would also permanently destroy the trust of your employees and customers.
The digitalization of your HR processes is an important step - but it must be based on an absolutely secure foundation. To understand the basic principles of data protection, which form the basis for GDPR-compliant operational planning, you can the general data protection declaration see. This guide will help you ask the right questions and make an informed decision about a secure and legally compliant cloud platform.
What really makes a secure cloud platform
Before we look at different providers for your operational planning, we have to define the rules of the game. What exactly does “secure” and “GDPR compliant” mean in practice? Marketing slogans always sound good, but in the end it is the details that determine liability risks and significant fines.
That's why we're now taking a closer look at the crucial criteria that you have to check mercilessly with every provider. With this knowledge, you can see through the marketing blah blah and make an informed, fact-based decision for your company.
Evaluation checklist for cloud providers in deployment planning
Use this checklist to quickly assess the suitability of cloud platforms and review key privacy and security considerations.
| criterion | Minimum requirement (GDPR compliant) | Optimal (Swiss standard & best practice) | Why it matters |
|---|---|---|---|
| Data location | Server location in the EU/EEA. | Server location exclusively in Switzerland or Germany with a local provider without a US connection. | Prevents access by foreign authorities (e.g. via the US CLOUD Act) and ensures compliance with local data protection laws. |
| Encryption | TLS encryption (In-Transit) and AES-256 (At-Rest). | Additional end-to-end encryption, where even the provider does not have access to the data. | Protects sensitive employee data from unauthorized access, both during transmission and at rest. |
| IAM & logging | Role-based rights management and basic access protocols. | Granular rights system, two-factor authentication (2FA) and complete, audit-proof audit logs. | Ensures that only authorized people access data and that all activities are traceable. |
| Certificates | Valid ISO 27001 certification. | Additional industry-specific certificates (e.g. SOC 2, C5) and regular, independent penetration tests. | Independent confirmation that the provider adheres to established security standards and has its processes audited. |
| Contractual (DPA) | Standardized order processing agreement (AVV/DPA). | Detailed DPA that clearly regulates liability issues, guarantees short response times in the event of security incidents and transparently lists all subprocessors. | The DPA is your legal shield. It defines the provider's obligations and protects you in the event of damage. |
| Subprocessors | Subprocessor Disclosure. | Detailed list of subprocessors with location and purpose. Contractual assurance that no critical data will be transmitted to third countries. | Transparency across the entire data processing chain is crucial in order to exclude hidden risks from third-party providers. |
This checklist is your compass. If a provider fails to meet the minimum requirements, you should pay attention. The optimal criteria show you who is really serious about it.
1. Server location is more than just an address
The physical location of the servers on which your employee data is stored is the be-all and end-all. A provider that advertises “servers in Europe” often only offers false security. Why? Laws like that US CLOUD Act allow US authorities to access data even if it is stored on European servers owned by US companies.
This is a huge legal risk that many underestimate. For maximum security you need a provider whose server demonstrably in Switzerland or Germany and which itself is not subject to the jurisdiction of data-hungry third countries.
My clear recommendation: A Swiss or German server location with a local provider is the safest choice to exclude access by foreign authorities. A general “EU location” with a US provider is simply not enough.
Imagine you are planning to deploy healthcare or security personnel. Passing on this data to foreign authorities without a legal basis would be a massive breach of trust and a clear violation of the law.
2. Not all encryption is created equal
Almost every provider speaks of encryption. Most of the time, this only means security during transmission (TLS) - that is absolute standard, but far from enough.
What you really need is consistency End-to-end encryption. This means: The data is already encrypted on your device and only made readable again by the authorized recipient. In addition, the data must also be encrypted on the server when at rest, this is referred to as encrypted “Encryption at Rest”.
- Encryption during transmission (In-Transit): Protects data between your computer and the server. Default is here TLS 1.2 or higher.
- Encryption at rest (At-Rest): Secures the data stored on the servers. At least that should be the case here AES-256 standard are used.
- End-to-end encryption: Offers the ultimate protection because even the cloud provider has no access to your unencrypted data.
A good one https://job.rocks/Einsatzplanungssoftware/ should be able to clearly document and demonstrate these protective mechanisms. Ask specifically about it!
3. Legal framework and certificates
Contracts and certificates are not annoying formalities, they are your legal shield. They prove that a provider takes its responsibility seriously. Be sure to pay attention to these points:
- Order processing contract (AVV/DPA): This contract is required by law and regulates the rights and obligations between you (the controller) and the cloud provider (the processor). Without a valid AVV, using the platform is simply illegal.
- Transparent subcontractors: The provider must state clearly which other service providers (subprocessors) he uses and where they process their data. Hidden US contractors are a red flag.
- Recognized certifications: Seal of quality like ISO 27001 or SOC2 are more than just logos. You confirm that a provider has had its security processes thoroughly checked by an independent body.
Anyone who wants to delve deeper into the subject will find valuable insights into the specific challenges of SaaS and data protection with data security. Only when all these factors fit together does the overall picture of a truly trustworthy platform emerge.
Cloud providers in direct comparison for your deployment planning
Now it's time to get down to business. You know the criteria you should use to choose a cloud platform for your GDPR-compliant deployment planning have to evaluate. Now we compare the large international providers with the specialized European and Swiss solutions. What exactly are the differences and which choice is the safest for you?
Die Entscheidung zwischen einem globalen "Hyperscaler" und einem lokalen Spezialisten ist keine reine Preisfrage. Es geht um rechtliche Garantien, Datenhoheit und das Vertrauen deiner Mitarbeitenden und Kunden. Schauen wir uns die Stärken und Schwächen der verschiedenen Modelle einmal genauer an.
US hyperscalers like AWS and Azure: A residual risk despite EU servers
Providers like Amazon Web Services (AWS) or Microsoft Azure are technological leaders and offer a huge range of services. They operate data centers in Europe, often even in Germany, and actively promote GDPR compliance. That sounds good at first glance, but there is a crucial catch.
As US corporations, both companies are subject to American law, in particular CLOUD Act. This law obliges them to grant US authorities access to stored data upon request. This obligation to release data applies regardless of where in the world the data is physically located - including on servers in Frankfurt or Zurich.
For your operational planning, this means a residual risk that should not be underestimated. Even if you contractually cover everything, the provider may be legally forced to disclose sensitive personal data about your employees.
European providers like OVHcloud and Hetzner: A solid alternative
European cloud providers like OVHcloud (France) or Hetzner (Germany) offer an interesting alternative. Since they are headquartered in the EU, they are not directly subject to the US CLOUD Act. Your business practices and contracts are adapted from the ground up to the strict requirements of the GDPR.
They often offer better value for money and a more transparent approach to subcontractors. They are a very good and legally secure choice for many standard applications in operational planning, as data access by non-EU authorities is significantly more difficult.
- Advantages: Clear GDPR alignment, no direct US government access, often more cost-effective.
- Disadvantages: Sometimes less functionality than hyperscalers, support not always at the same level.
Imagine organizing staff for a political event. The names and locations of employees are highly sensitive information. Relying on a European provider significantly minimizes the risk of unwanted data being passed on to foreign bodies.
These providers offer a good balance of security, functionality and cost for companies looking for a solid GDPR-compliant solution.
Swiss providers like Exoscale or nine.ch: The safest bank for sensitive data
For companies that require maximum data security and confidentiality, Swiss cloud providers are often the best choice. Hosters like Exoscale or nine.ch combine the advantages of a European legal area with the particularly high level of data protection in Switzerland.
The servers are located exclusively in Switzerland and the companies are subject to Swiss law. This creates an additional protective wall against access requests from abroad.
This decision tree helps you choose a cloud platform by walking you through important questions like server location, encryption, and certificates.
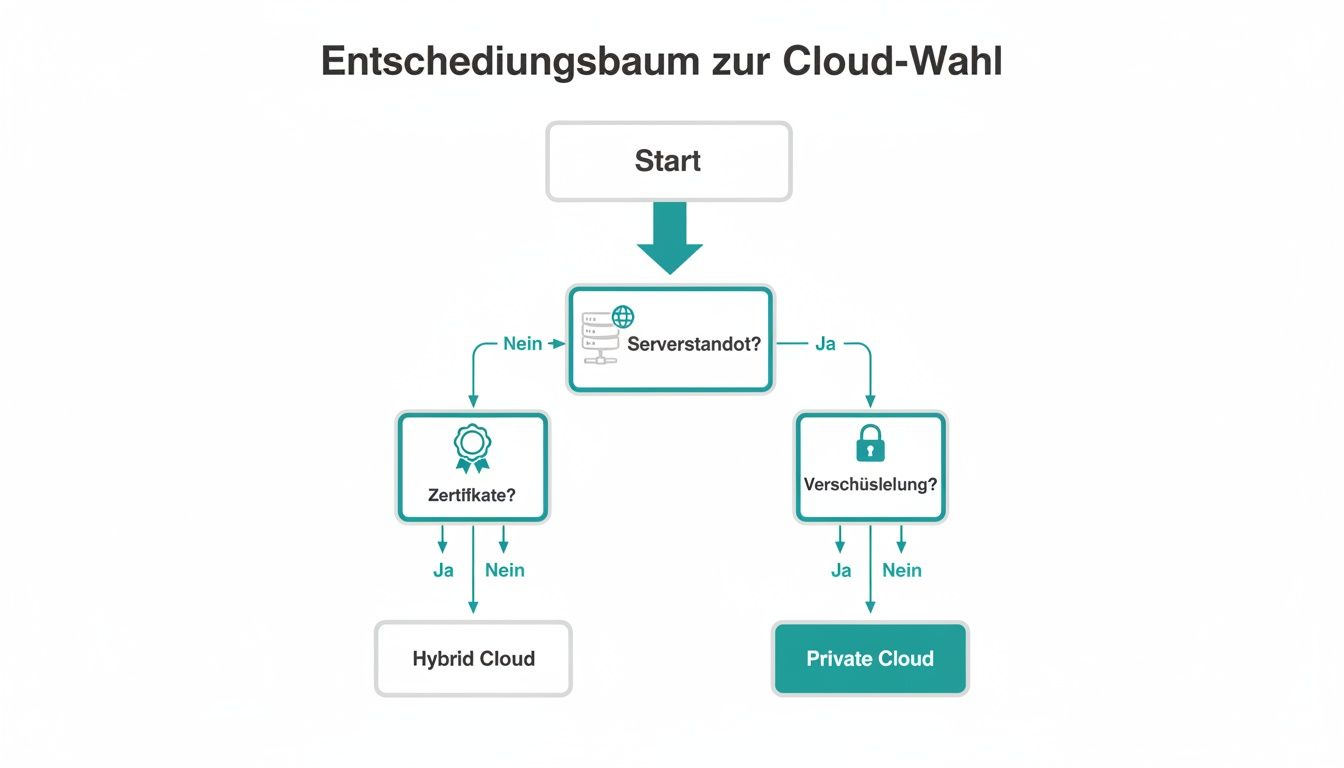
The visualization makes it clear that choosing a provider depends on your company's specific security needs, with local providers often meeting the most stringent criteria.
The aforementioned US Cloud Act in particular poses a significant data protection risk for Swiss companies, which must be taken into account when selecting cloud platforms. The Conference of Swiss Data Protection Commissioners (Privatim) has made this clear and actually recommends abandoning international cloud services for sensitive data. The reason: The US Cloud Act forces American providers to hand over personal data to US authorities, even if the data is located in Switzerland. This legal situation contradicts the strict Swiss data protection principles. Find out more about the Recommendations from Swiss data protection officers on international cloud services.
Which provider fits which scenario?
The best choice depends on your specific use case and your risk tolerance. Here are some real-world examples:
-
Scenario 1: Event agency with international staff
You are planning assignments for a music festival with hundreds of freelancers from all over Europe. The data includes names, contact details and availability.
Recommendation: A European provider like Hetzner is an excellent choice here. You safely meet the GDPR requirements, benefit from fair prices and avoid the legal uncertainties of US providers. -
Scenario 2: Catering business with temporary staff
Your restaurant coordinates flexible temporary staff via an app. The data is less critical than in healthcare, but still needs to be protected.
Recommendation: Here too is one European provider often the best balance. However, if you want to be on the safe side and your budget allows it, offer a Swiss host additional security. -
Scenario 3: Critical infrastructure security service
You plan the staff for banks, airports or government buildings. The data is extremely sensitive and is subject to the strictest confidentiality requirements.
Recommendation: There are no compromises here. A Swiss provider like exoscale is the only sensible choice. Any access to data by foreign bodies must be excluded, and only local providers under Swiss jurisdiction can guarantee this.
Finding the right platform for your GDPR-compliant operational planning is a strategic decision. Weigh the technological possibilities against the legal guarantees and choose the provider that offers the level of protection your sensitive employee data deserves.
Practical examples: Which cloud platform is really right for you?
Theory is one thing, but practice is crucial. Let's go through the whole thing using three typical scenarios that you probably know from everyday work. These examples quickly make it clear how different the requirements are GDPR-compliant deployment planning are – and how they directly influence the choice of cloud provider.
These simulations help you reflect your own needs. This way you can find a solution that is not only secure, but also functional and scalable.
Scenario 1: The event agency with hundreds of freelancers
Imagine you run an events agency that throws large festivals and corporate events. Your personnel pool? Hundreds of freelancers – technicians, hostesses, logistics helpers. A huge, dynamic bunch.
Your challenges:
- Mass communication: You have to query availability in record time and ask hundreds of people for shifts at the same time.
- Qualification management: Every job has different skills. You must ensure that only staff with the correct certificates (e.g. forklift license, medical training) are booked.
- Data sensitivity: Names, addresses, bank details, proof of qualifications – you process all of this. The data is sensitive, but not highly critical in the sense of state secrecy.
What does that mean for the cloud?
Your focus is clearly on scalability and the efficient management of huge amounts of data. Data protection has to be right, of course. But you don't need the same precautions as a bank.
Your priority is a provider that fully complies with the GDPR, but at the same time has the technical power for mass bookings. A US provider with EU servers would technically be an option, but always carries the residual risk of the CLOUD Act.
My recommendation: A European cloud provider How OVHcloud or a German provider like Hetzner is the ideal choice here. You get a legally secure platform without US government access that is cost-effective and strong enough for your needs.
Scenario 2: The catering business with flexible temporary workers
Now let's change perspective: You are a restaurant owner and your staffing needs fluctuate massively depending on the season and day of the week. You juggle with a pool of students and temporary staff, who you often have to schedule at short notice.
Your challenges:
- Short-termism: If someone fails, you often have to find a replacement within a few hours.
- Easy to use: Planning takes place via a simple, mobile app. It also has to be understandable for people who don't have much to do with technology.
- Time recording: Working times must be recorded down to the minute and clearly transmitted to payroll.
What does that mean for the cloud?
You process standard personal data: name, contact, working hours. The biggest priority here is reliability and simplicity of use. Data protection must be solid, but the complexity is significantly lower than with the event agency.
My recommendation: Here too you drive with one European provider very good and safe. Your data is protected within the EU and the costs remain manageable. A Swiss provider would be an option if you value maximum data security and the budget allows it - but it is not absolutely necessary for this scenario.
Scenario 3: The security service for critical infrastructure
Finally, the most demanding scenario. You are responsible for the operational planning of a security service that provides staff for banks, airports and government buildings. This is where we get down to business.
Your challenges:
- Highest confidentiality: The names of employees, their locations and shift schedules are extremely sensitive information. A data leak could have catastrophic consequences.
- Strict compliance: Not only are you subject to the GDPR, but you are often also subject to additional, industry-specific security requirements.
- Obligation to provide proof: Every personnel change, no matter how small, must be recorded completely and in an audit-proof manner.
What does that mean for the cloud?
There is absolutely no room for compromise here. Data sovereignty and protection against any unauthorized access are top priority – especially by foreign authorities. The US CLOUD Act is an absolute knockout criterion.
My recommendation: A Swiss cloud provider How Exoscale or nine.ch is the only justifiable solution. Only a provider that is subject exclusively to Swiss law and operates its servers in Switzerland can guarantee the required level of protection. Any alternative, whether European or American, would be an unacceptable risk in this context. The choice of cloud platform is a fundamental part of your security concept.
What the use of AI means for your data protection-compliant personnel planning

Artificial intelligence has become an integral part of modern operational planning. It optimizes shifts, predicts staffing requirements and suggests the right employees for a job. But as soon as algorithms start making decisions about people, data protection alarm bells start ringing.
When AI-powered software like job.rocks automatically makes recommendations about who should fill a shift, we're in the realm of automated individual decision. Both the GDPR and the revised Swiss Data Protection Act (revDSG) place high demands on this - especially in terms of transparency and traceability.
The data protection impact assessment as a mandatory exercise
As soon as you use technologies that pose a high risk to people's fundamental rights and freedoms, a Data Protection Impact Assessment (DPIA) to duty. The use of AI in personnel planning almost always falls into this category, because the risk that algorithms will unnoticed favor or disadvantage employees is real.
A DPIA is essentially a systematic risk analysis. You must document exactly:
- Which personal data is processed and how.
- What risks could arise for those affected (e.g. discrimination in shift allocation).
- What measures do you take to reduce these risks to a minimum?
Imagine an algorithm scheduling a particular person for lucrative weekend shifts less often because it has learned from old data that this person used to cancel at short notice more often. Without human control, this could lead to unfair treatment that no one notices.
Such an assessment is not a one-time act. It must be checked regularly, especially if you introduce new AI functions or the processing processes change fundamentally.
Transparency in automated decisions
Probably the most important point is this Obligation to provide information. You must clearly and understandably inform your employees that automated decisions are taking place. It is your right to know what logic the algorithm uses and what consequences this has for you.
Let’s assume you use AI to optimize the route of your delivery service. The software automatically assigns drivers the most efficient routes. In this case, you must make it transparent which factors (e.g. traffic situation, vehicle type, expected delivery time) influence the decision. Even more important: Those affected must have the opportunity to have the decision reviewed by a human.
This need for control reflects a broad societal expectation. A 2023 study by MISTREND shows that 80% of Swiss people call for greater government regulation of the use of AI. This underlines the high level of data protection awareness that directly impacts the requirements for cloud platforms for workforce management.
When using AI, choosing a trustworthy Swiss or European provider becomes even more crucial. Such a partner must not only guarantee a secure infrastructure, but also provide the necessary transparency and documentation so that you can fully fulfill your legal obligations. Find out more about this in our complete guide to workforce management.
Your checklist for implementation and migration
You’ve chosen a secure, GDPR-compliant cloud platform – great! But the real work is just beginning. A chaotic migration quickly leads to data loss, downtime and demotivated employees.
This checklist is your compass through the transition process. It helps you avoid legal pitfalls and set up the technology cleanly. This means that switching to your new deployment planning solution will be a guaranteed success.
Phase 1: Internal preparation and communication
The first step doesn't happen in the system, but in the minds of your team. A well-informed group of employees is the basis for every successful change.
- Communicate the “why”: Explain to your team clearly and comprehensibly why you are changing the platform. Highlight the specific advantages, such as more data security, leaner planning processes or the better mobile app for employees.
- Put together a project team: Identify crystal clear responsibilities. Who is the technical contact? Who takes care of the training? And who is responsible for legal clearance?
- Create a schedule: Define realistic milestones. When do we start data migration? When do the trainings take place? When is the official go-live date?
A transparent approach creates acceptance and ensures that everyone pulls together.
Phase 2: Legal and contractual review
Before you upload a single employee file, the legal framework must be watertight. This point is non-negotiable because the greatest risks lurk here.
The best technical protection is worthless without a clear contractual basis. The order processing agreement (AVV) is your legal protective shield - it defines the provider's obligations when dealing with your sensitive personal data.
Check these documents like a hawk:
- Order processing contract (AVV): Is it complete and specific enough? Does it clearly regulate liability issues, reporting deadlines for data breaches and your control rights?
- General Terms and Conditions (GTC): Are there hidden clauses that contradict your rights or disadvantage you?
- List of subprocessors: Take a close look at which other service providers the provider uses. Are they based in unsafe third countries without an adequate level of data protection?
Phase 3: Technical migration and training
Now it's time to get down to business: the data. A clean migration is the best insurance against problems later in operation.
- Data cleaning: Take advantage of the opportunity to clean up your existing employee data. Finally delete the outdated contacts and correct incorrect entries.
- Perform test migration: First transfer only a small, non-critical data set. This way you can test the process without bringing the entire operation to a standstill.
- Train employees: Conduct practical training, not dry PowerPoint lectures. Show your team the new processes directly in the system so that they click immediately.
- Go live and support: It's best to plan the final move for a time when there is less traffic, for example overnight or on the weekend. Very important: Make sure that a competent contact person is available to answer any questions in the first few days after the change.
Frequently asked questions about GDPR-compliant deployment planning
Here we clarify the most burning questions about secure cloud platforms and data protection in personnel planning. Consider this section your shortcut to the most important answers for one GDPR-compliant deployment planning.
Is a server location in the EU really enough?
A server location in the EU is the absolute minimum requirement, but that is often only half the battle. If the cloud provider is a US company - as is the case with AWS, Microsoft Azure or Google Cloud - it is subject to this US CLOUD Act. This law potentially gives US authorities access to your data, even if it is physically located in a data center in Frankfurt or Dublin.
If you want to be on the safe side with sensitive personnel data, choose a provider with headquarters and servers in Switzerland or Germany. This means that this residual legal risk can be eliminated from the outset.
What is the difference between GDPR and the revDSG?
Both laws have the same goal: the protection of personal data. But the focuses are different. The GDPR (General Data Protection Regulation) is the set of rules for the entire EU and has a very broad scope.
The revised Swiss Data Protection Act (revDSG) applies specifically to Switzerland and is even stricter in some points. A crucial difference lies in personal liability: In Switzerland, the responsible private individual can face a fine of up to 250,000 CHF be prosecuted, which massively increases personal responsibility.
Do I have to sign an AV contract for every piece of software?
Yes, without exception. As soon as an external service provider (i.e. your cloud provider) processes personal data on your behalf, a Order processing agreement (AVV) mandatory by law. This applies to your deployment planning software as well as to your newsletter tool or payroll accounting.
Without a valid AVV, using the service is simply illegal. The contract is your legal shield and clearly states what the provider is allowed to do with your data - and what is not.
Can I send employee data via email?
Basically yes, but only under very strict conditions. A normal, unencrypted email is absolutely taboo for sending personnel data such as rosters or pay slips. It's as safe as a postcard.
You must guarantee that the data is protected throughout the transfer. The best way to do this is:
- End-to-end encryption the email itself.
- Using secure portals that allow employees to download documents instead of sending them directly as attachments.
Find out more here. One wrong click can trigger a reportable data protection incident and have serious consequences.
Would you like to set up your operational planning from the ground up to be secure and GDPR-compliant? job.rocks offers you a workforce management platform that runs on Swiss servers and meets the highest data protection standards. Book your personal demo now and find out how you can make your processes legally compliant and more efficient. Visit us https://job.rocks.
